Cooking with SIMD

When developers gather around a screen like in this picture, you know something special is cooking. We're very excited about our prototyping with single instruction, multiple data (SIMD) processing, but this newsletter is not about that yet (nor about better kerning). More on that soon! Now, with the summer break behind us we're back in top gear and excited to bring you a packed update. Let's dig in!
💬 In this issue:
- Policy & Governance: We are closely following a legislative proposal by the European Commission affecting almost all hardware and software on the European market.
- Routinator: Please upgrade to resolve a CVE. Also, ARIN updated their Relying Party Agreement, simplifying the use of their Trust Anchor in our software.
- Krill: We've released BGPsec and HSM support, added improved details about your ROA configurations and there are upcoming speed improvements.
- Unbound: We released a fix for the NRDelegation Attack. ACLs per interface and the PROXYv2 protocol are coming up in the next release.
Policy & Governance
We are closely following a legislative proposal by the European Commission affecting almost all hardware and software on the European market. The Cyber Resilience Act intends to ensure cybersecurity of products with digital elements by laying down requirements and obligation for economic operators.
We want to make sure that policy makers take into account its effects on open source development by professional organisations and volunteers alike, and plan to make ourselves heard. Do get in touch with Maarten when you have similar concerns, want to team up or can help us to provide technical expertise in the right places.
Routinator
First things first: please update your Routinator to the latest release, version 0.11.3. This fixes a vulnerability assigned CVE-2022-3029 affecting version 0.9.0 up to and including 0.11.2. It causes Routinator to exit if it encounters invalid data in RRDP snapshot or delta files.
ARIN announced they made changes to the management of their Trust Anchor Locator (TAL) for RPKI. The intent is that Relying Party software vendors can ship and use the ARIN TAL by default, and no longer require users to provide explicit consent. This will simplify initialisation for Routinator and will be especially nice for use in unattended environments. We aim to make this available in the next release.
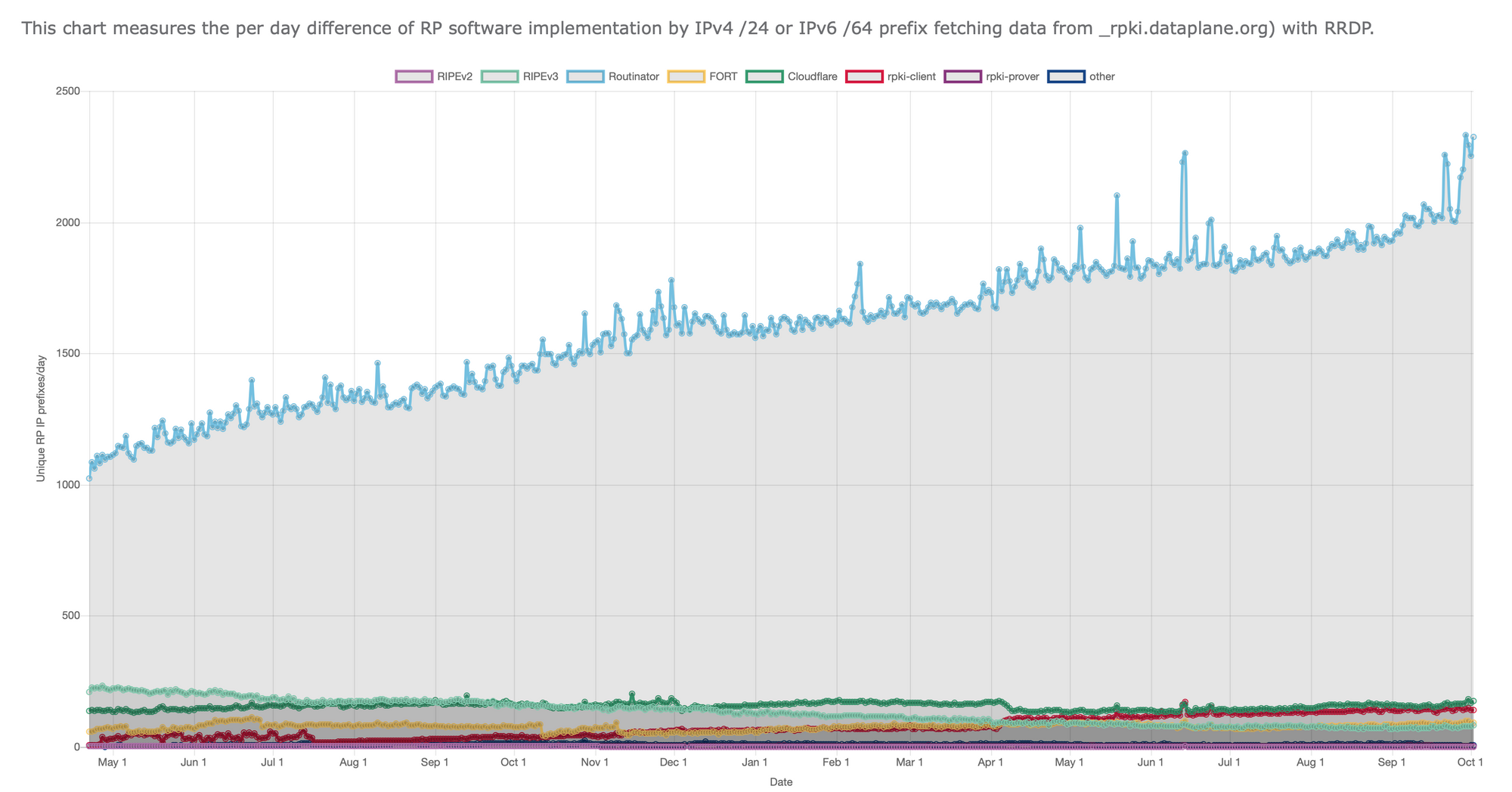
Lastly, we're excited to tell you that over 2000 networks are now running Routinator for RPKI Route Origin Validation. Thank you all for the trust and support!
Krill
We've got a pretty major announcement on the horizon for Krill, but before we can do that we're going through a series of smaller releases. In Krill 0.10.0 released several weeks ago we added BGPSec Router Certificate Signing and support for the use of Hardware Security Modules (HSMs) for key operations.
Krill has been designed with the idea of "ROA configurations". This means that you just have to specify which routes are authorised, and Krill will create and automatically renew the cryptographic objects to achieve this. Because some operators would like to know what is happening in the background, version 0.11.0 adds the ability to show which ROA objects were created for each ROA configuration. It also adds support optional comments for each ROA configuration.
Now we're gearing up for the next release which will focus on significantly improving Krill's speed. We are running the Krill CA and publication server on a single, modest system for benchmarking. Using it, we are targeting that version 0.12.0 will be capable of running 5000 CAs with ten ROAs each while remaining responsive.
Unbound
Various DNS resolving software packages, including Unbound, are affected by a vulnerability named Non-Responsive Delegation (NRDelegation) Attack. We have assigned CVE-2022-3204 and categorise this a medium severity for Unbound. A fix is available in version 1.16.3, so please upgrade as soon as possible.
Meanwhile, the development pipeline is filling up with a plethora of new features. We have recently merged support for ACLs per interface and the PROXYv2 protocol. In an upcoming release we'll also offer downstream DNS server cookies and Extended DNS Error caching.
🗞 From the News Desk
- We've released version 0.7.0 of our domain crate, forming a springboard for using generic associated types (GATs) – a rather big and exciting thing in Rustland.
- Rotonda, our modular BGP engine, will have a dynamic, interpreted language for data modelling (programmable RIBs), querying and filtering routes.
- Kindred spirits in Rust, we're excited to kick off a partnership with Tweede golf, specialists in writing safe and privacy-friendly software. Stay tuned!
- Come say hi! In the coming weeks we'll participate in the One Conference in The Hague, OARC 39 and RIPE 85 in Belgrade, and IETF 115 in London.
Thanks for reading, until next time!
Love from the NLnet Labs crew

